Windows 10 Critical Patch (Click Here for Download Links)
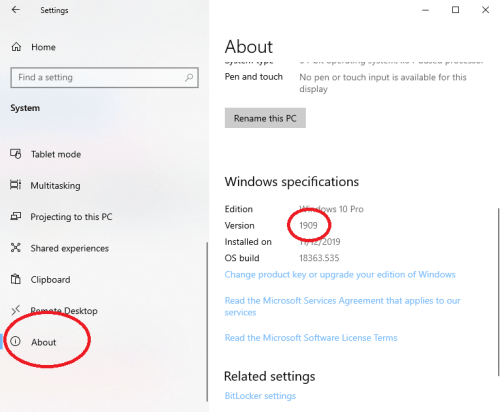
Windows Update may not automatically install this patch so it is recommended to manually install this update if it doesn’t show in your installed updates. Please ensure you select the correct version of Windows. To check which version of Windows 10 you’re using follow these instructions:
- Click “Start”
- Click “Settings”
- Click “System”
- Scroll down and Click “About” than scroll down to find your version
——————————————————————————————-
——————————————————————————————-
CVE-2020-0601 | Windows CryptoAPI Spoofing Vulnerability
January 14, 2020
A spoofing vulnerability exists in the way Windows CryptoAPI (Crypt32.dll) validates Elliptic Curve Cryptography (ECC) certificates.
An attacker could exploit the vulnerability by using a spoofed code-signing certificate to sign a malicious executable, making it appear the file was from a trusted, legitimate source. The user would have no way of knowing the file was malicious, because the digital signature would appear to be from a trusted provider.
A successful exploit could also allow the attacker to conduct man-in-the-middle attacks and decrypt confidential information on user connections to the affected software.
The security update addresses the vulnerability by ensuring that Windows CryptoAPI completely validates ECC certificates.
SOURCE = Microsoft
——————————————————————————————-
——————————————————————————————-
Windows 10: NSA reveals major flaw in Microsoft’s code
Jauary 14, 2020
Microsoft has issued a patch and said it had seen no evidence of the bug being exploited by hackers. The issue was revealed during an NSA press conference. It was not clear how long it had known about it before revealing it to Microsoft. Brian Krebs, the security expert who first reported the revelation, said the software giant had sent the patch to branches of the US military and other high-level users ahead of its wider release.
It was, he wrote, “extraordinarily scary”. The problem exists in a core component of Windows known as crypt32.dll, a program that allows software developers to access various functions, such as digital certificates which are used to sign software. It could, in theory, have allowed a hacker to pass off a piece of malicious software as being entirely legitimate.
SOURCE = BBC News
——————————————————————————————-
——————————————————————————————-
Microsoft, NSA confirm killer Windows 10 bug, but a patch is available
January 14, 2020
As expected, Microsoft did reveal a fundamental flaw in Windows that affected Windows 10’s cryptographic library. January’s Patch Tuesday updates issued today, however, fix the issue, which is specific to Windows 10 and Windows Server. The flaw, CVE-2020-0601, was found in the usermode cryptographic library, CRYPT32.DLL, that affects Windows 10 systems. (Contrary to earlier rumors, it does not affect Windows 7, which coincidentally is being shut down Tuesday as well.) Fortunately, Microsoft reported that the library was not in active use, though that doesn’t prevent an attacker from weaponizing it now that it’s been disclosed.
“Exploitation of the vulnerability allows attackers to defeat trusted network connections and deliver executable code while appearing as legitimately trusted entities,” the NSA said. “Examples where validation of trust may be impacted include: HTTPS connections, signed files and emails, [and] signed executable code launched as user-mode processes.”
Specifically, the attack could allow malware to hide behind a spoofed cyrptographic signature. Antivirus software could therefore identify malware as legitimate applications, or fake banking sites could use the vulnerability to trick a user’s PC into thinking it was legitimate. Microsoft did not cite the source that reported the vulnerability. The Washington Post had reported that the National Security Agency (NSA) had developed the exploit, then turned it over to Microsoft. The NSA itself took credit for the discovery in a security advisory released Tuesday. Specifically, CVE-2020-0601 will affect Windows 10, according to Microsoft. The NSA believes it will affect Windows Server 2016/2019 as well.
SOURCE = PC World